Basic Concept of System Model of Deadlocks:
The sequences by which a process may utilize a resource / the basic concept of the system model of deadlocks are as follows:
- Request: If the request cannot be granted immediately, then the requesting process must wait until it can acquire the resource.
- Use: The process can operate on the resource.
- Release: The process releases the resource.
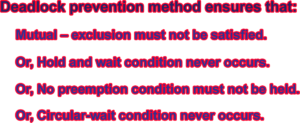
Methods of Deadlock Prevention:
Deadlock prevention is a set of methods for ensuring that at least one of the necessary conditions for deadlock (such as mutual exclusion, hold and wait, no-preemption circular wait) does not occur in the system. The methods of deadlock prevention ensure that:
Mutual-exclusion: The mutual-exclusion condition must hold for non-sharable resources such as a printer. On the other hand, shareable resource tools not require mutually exclusive access and thus cannot be involved in the deadlock. Read-only files are a good example of a shareable resource. In general, it is not possible to prevent deadlock by denying the mutual-exclusion condition.
Hold and wait: to ensure that the hold-and-wait condition never occurs it the system, we must guarantee that, whenever a process requests a resource, it does not hold any other resources. To achieve this, we can use two protocol:
- One protocol requires each process to request and be allocated all its resources before it begins exclusion.
- Other protocols allow a process to request resources only when the process has none.
No-preemption: to ensure this condition does not hold, we can use the following protocol.
If a process holding some resources and requests another resource that cannot be immediately allocated to it (this is, the process must wait), then all resources currently being held are preempted. These resources are implicitly released.
Alternatively, if a process requests some resources, if the resources are available, they are allocated them. If they are not available, we check whether they are allocated to some other process that is waiting for additional resources. If so, we preempt the desire resources from the waiting process and allocated them to the requesting process. If the resources are neither available non-held by a waiting process, the requesting process must wait.
Circular wait: to ensure that circular-wait never held, it is to impose a total ordering of all resource types and require that each process requests resources in increasing order of enumeration.
This resource is uniquely numbered. Consider the following:
Tape drive 1
Disk drive 2
Printer 3
A process may request first tape drive then disk drive but it may not request first disk drive then tape drive.
Alternatively, a process can request any number of an instance of resource type Rj, it has released any resource Ri such that F (Ri) ≥ F (Rj).
Therefore, there can be no circular wait.
At this time, the system is in a safe because there exists a safe sequence <P1, P0, P2> since P1 can get immediately all its tape drives and then return them. Then P0 can get all its tape drives and return them.
But at time t1, if process P2, requests and it allocated one tape drive then the system must be in an unsafe state because no process can finish its execution for an indefinite period of time causing a deadlock.
Reference: Operating System Concepts written by Abraham Silberschatz, Peter Baer Galvin, and Greg Gagne.

Assistant Teacher at Zinzira Pir Mohammad Pilot School and College