Financial Crime Risk Management (FCRM):
Financial Crime Risk Management (FCRM) has become a critical aspect of organizational strategies worldwide. In an era where businesses are heavily reliant on digital platforms, the risk of financial crimes has escalated, necessitating proactive measures to safeguard against potential threats. In this article, we delve into the intricacies of FCRM, exploring various types of financial crimes, the role of Anti-Money Laundering (AML) and compliance, methods for performing a financial risk assessment, and the effectiveness of FCRM solutions.
What is FCRM?
Financial Crime Risk Management (FCRM) is the systematic practice of proactively identifying, assessing, and mitigating the risks associated with a broad spectrum of financial crimes, including but not limited to money laundering, fraud, bribery, corruption, and other illicit activities. FCRM involves the implementation of strategies, policies, and controls to safeguard organizations from the detrimental effects of financial crimes, ensuring compliance with regulatory standards and maintaining the integrity of financial systems.
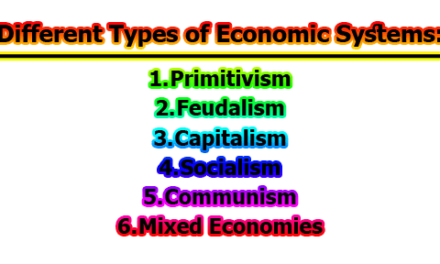
Types of Financial Crimes:
Financial crimes encompass a broad spectrum of illegal activities designed to exploit monetary systems for personal gain. Understanding these crimes is crucial for developing effective risk management strategies. Major types include:
1. Money Laundering:
Definition: Money laundering involves the process of concealing the origins of illegally obtained money, typically by means of transfers involving foreign banks or legitimate businesses.
Risk Implications: Money laundering poses a significant risk to the financial system by allowing illicit funds to enter mainstream circulation, making detection and tracing of criminal proceeds challenging.
2. Terrorist Financing:
Definition: Terrorist financing involves providing financial support to terrorist organizations or individuals with the intent of facilitating acts of terrorism.
Risk Implications: Funding terrorist activities threatens national security and stability, making it a critical focus area for financial crime risk management.
3. Fraud:
Definition: Fraud is the intentional deception to secure unfair or unlawful gain, often through false representation, manipulation, or other deceptive practices.
Risk Implications: Fraudulent activities, such as credit card fraud or identity theft, can result in financial losses for individuals and organizations alike.
4. Bribery and Corruption:
Definition: Bribery involves the offering, giving, receiving, or soliciting of something of value to influence the action of an official or other person in a position of authority.
Risk Implications: Bribery and corruption undermine fair business practices, erode public trust, and can lead to legal consequences for individuals and organizations involved.
5. Market Abuse:
Definition: Market abuse refers to actions that distort the proper functioning of financial markets, including insider trading, market manipulation, and spreading false information.
Risk Implications: Market abuse compromises the integrity of financial markets, erodes investor confidence, and can lead to market instability.
6. Insider Trading:
Definition: Insider trading involves trading in a security based on material, non-public information about the security.
Risk Implications: Insider trading undermines the fairness of financial markets, providing unfair advantages to those with privileged information.
7. Tax Evasion:
Definition: Tax evasion is the illegal act of not paying taxes owed to the government, often through concealing income, inflating deductions, or other fraudulent means.
Risk Implications: Tax evasion reduces government revenue, affecting public services, and can result in legal consequences for individuals and businesses.
8. Embezzlement:
Definition: Embezzlement involves the misappropriation or theft of funds entrusted to an individual, typically an employee, for personal use.
Risk Implications: Embezzlement can lead to financial losses for organizations and erode trust in internal controls.
9. Counterfeiting:
Definition: Counterfeiting involves the production of imitation goods, typically currency, with the intent to deceive and defraud.
Risk Implications: Counterfeiting undermines the stability of currency and can lead to economic distortions.
10. Identity Theft:
Definition: Identity theft is the unauthorized use of someone else’s personal information for fraudulent purposes, often to commit financial crimes.
Risk Implications: Identity theft poses a significant threat to individuals’ financial well-being and can result in reputational damage for organizations.
11. Electronic Crime:
Definition: Electronic crime, or cybercrime, involves criminal activities conducted through digital means, such as hacking, online fraud, and data breaches.
Risk Implications: With the increasing reliance on digital platforms, electronic crime poses a pervasive and evolving threat to individuals and organizations.
These crimes can be perpetrated by external entities, internal employees, or even high-ranking executives within an organization. Additionally, there are lesser-known financial crimes such as personal purchases, theft, skimming, payroll schemes, and billing schemes, all of which contribute to the overall landscape of financial risk.
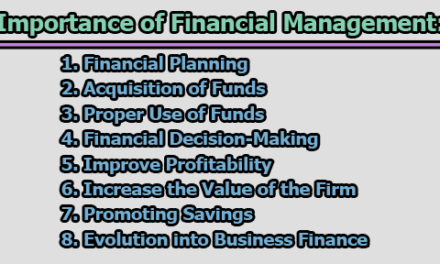
Financial Crime Compliance Costs:
Financial crime compliance ensures organizations adhere to standards, policies, and regulations, both internal and external. The compliance landscape has evolved over the years, with regulatory frameworks like the Bank Secrecy Act (BSA) and the USA PATRIOT Act shaping the field. However, compliance comes at a significant cost. The global expenditure on financial crime compliance reached $274 billion in 2022, marking a 28% increase from 2020. As financial crimes continue to rise, costs are anticipated to escalate in 2023.
Challenges and Best Practices in AML Compliance:
Anti-Money Laundering (AML) compliance has become progressively challenging due to technological advancements, increased financial crimes, and expanding regulations. Factors contributing to these challenges include the shift of products and services online, deprioritization of compliance, and the overwhelming volume of customer and transaction data. To navigate these challenges, organizations are advised to:
- Establish internal policies and procedures for preventing money laundering.
- Employ AML investigators and support them with efficient AML software.
- Provide ongoing training to employees on recognizing and reporting suspicious activities.
- Strictly maintain record-keeping and reporting practices.
Financial Risk Assessment:
A systematic financial risk assessment is imperative for identifying an organization’s vulnerabilities to financial crime. The following steps outline the process:
- Identify risks: Understand and document risks based on the organization’s complexity, market, products, and online presence. Prioritize risks according to their potential threat level.
- Establish protective measures: Plan and implement controls and systems to mitigate identified risks. This includes assigning responsibilities, creating organization-wide policies, and implementing Customer Due Diligence (CDD) and Enhanced Due Diligence (EDD).
- Review and improve controls: Conduct regular audits to ensure controls are addressing new risks and update procedures and policies accordingly.
- Monitor and report: Regularly monitor the effectiveness of controls, document suspicious activities, and ensure compliance with reporting requirements.
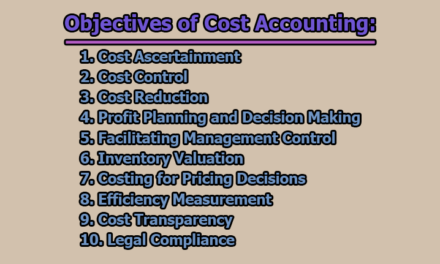
Financial Crime Risk Management (FCRM) Systems:
FCRM tools play a crucial role in proactively identifying vulnerabilities, continuously monitoring activity, conducting risk assessments, and responding to suspicious behavior. Key capabilities include:
- Real-time threat detection: Instantly identify suspicious activity and alert security personnel for timely response.
- Anomalous user behavior detection: Utilize advanced analytics and machine learning to detect unusual behavior associated with users, devices, and applications.
- Efficient investigation: Quickly search through vast amounts of current or historical data to uncover financial crimes.
- Alert management: Establish custom rules and automation to reduce alert fatigue and false positives.
- Compliance adherence: Bring order to unstructured data to meet fraud and AML compliance regulations.
- Analytics and reporting: Analyze, measure, and manage financial crime risks while sharing critical information with stakeholders.
FCRM Systems in Action:
Let’s explore how FCRM systems operate in action to protect businesses and ensure compliance with regulatory requirements.
1. Electronic Payment Fraud:
Detection and Prevention: FCRM systems leverage real-time threat detection to identify anomalies in electronic payment transactions. These anomalies could include unusual transaction amounts, irregular frequencies, or transactions from unfamiliar locations.
Behavior Analysis: Advanced analytics and machine learning enable FCRM systems to analyze user behavior associated with electronic payments. Any deviation from established patterns triggers alerts for further investigation.
2. Fraud:
Cross-Channel Data Aggregation: FCRM tools continuously aggregate data from various channels, creating comprehensive behavior profiles for customers and accounts. This cross-channel analysis helps identify patterns indicative of fraudulent activities.
Automatic Pattern Recognition: FCRM systems automatically scan for unusual behavior and key indicators of fraud risk. This proactive approach allows organizations to detect and respond to potential fraud before significant damage occurs.
3. Electronic Crime:
Custom Rules and Alerts: FCRM systems empower organizations to set up custom rules and alerts tailored to specific types of electronic crime. This customization reduces alert fatigue by focusing on relevant threats.
Investigation Efficiency: With the ability to quickly search through vast amounts of data, FCRM tools streamline the investigation process, enabling security personnel to identify and address electronic crimes promptly.
4. Money Laundering:
AML Capabilities: FCRM systems equipped with Anti-Money Laundering (AML) capabilities use historical data to pinpoint suspicious patterns in customer transactions.
High-Risk Individual Identification: These systems aid in identifying high-risk individuals involved in money laundering activities, ensuring organizations can take preventive measures.
5. Terrorist Financing:
Sanction List Checks: FCRM solutions often include features to check activities against sanction lists. If a match is found, the system can hold payments until further verification or authorization is obtained.
Real-time Monitoring: Continuous monitoring of financial activities helps identify potential links to terrorist financing, allowing organizations to report and take necessary actions.
6. Bribery and Corruption:
Connection Identification: FCRM tools assist investigators in identifying connections between contractors, public officials, and other entities, pinpointing unusual payment patterns indicative of bribery and corruption.
Pattern Analysis: Through pattern analysis, these systems can highlight irregularities in financial transactions, raising red flags for potential corrupt practices.
7. Market Abuse and Insider Dealing:
Employee Trade Monitoring: FCRM solutions help organizations manage and monitor employee trades. Real-time comparison against activities in the securities market enables the identification of potential insider dealing or market abuse.
Illegal Trading Investigation: By providing insights into employee transactions, FCRM systems aid in investigating and preventing illegal trading activities within the organization.
Best Practices for Financial Crime Risk Management:
To effectively manage financial crime risk, organizations should adhere to legal precedents and implement best practices. Key recommendations include:
- Stay informed about relevant laws and regulations.
- Monitor changes in laws and build awareness within the organization.
- Implement internal policies and procedures to prevent financial crimes.
- Choose the right FCRM solution based on organizational needs.
- Prioritize reliable and complete data, customized dashboards, regulatory compliance features, and user-friendliness when selecting an FCRM solution.
In conclusion, the landscape of financial crime is evolving, necessitating robust Financial Crime Risk Management strategies. Organizations must be proactive in identifying, preventing, and responding to financial crimes to mitigate risks and ensure compliance with regulations. Implementing effective FCRM solutions, conducting thorough risk assessments, and staying abreast of compliance requirements are crucial steps in safeguarding financial integrity in today’s interconnected and digital business environment.

is an experienced educator and academic currently serving as a Lecturer at Nurul Amin Degree College. With a career dedicated to student development and institutional excellence, he brings a wealth of classroom expertise and pedagogical knowledge to his current role. Before joining the faculty at Nurul Amin Degree College, he served as an Assistant Teacher at Zinzira PM Pilot School and College.